When Every Second Counts: How SecureClaw's Digital Forensics-as-a-Service (DFaaS) Accelerates Cyber Investigations
The cost of delaying or improperly handling forensic reports following cyber attacks is demonstrated by a number of actual enforcement actions. The SEC fined the main business of the New York Stock Exchange, Intercontinental Exchange (ICE), $10 million for failing to disclose a cybersecurity compromise. Regulators pointed out that ICE breached obligatory incident-reporting standards and neglected to swiftly alert legal and compliance departments, highlighting the necessity of timely forensic evidence and breach documentation. In a similar vein, the SEC penalized twelve significant financial companies, including Blackstone, KKR, Schwab, Apollo, and Carlyle, $63.1 million for recordkeeping violations that hindered their ability to produce and preserve necessary electronic communications. This illustrates how failing to maintain forensic-grade digital evidence becomes a compliance violation in and of itself. In a different instance, regulators fined Infosys McCamish Systems for failing to promptly report a ransomware breach and for not having the necessary cybersecurity controls.
This underscores the regulatory requirement that organizations maintain timely, comprehensive incident evidence that is in line with forensic standards. These cases collectively demonstrate that businesses risk serious compliance, legal, and financial consequences when they are unable to create timely, accurate digital forensics records - whether as a result of missing logs, delayed reporting, or poor evidence retention.
Recent enforcement actions highlight this trend, such as the U.S. Department of Health and Human Services’ OCR issuing 19 HIPAA settlements totaling over $8 million in 2025, driven largely by inadequate risk analysis, poor access controls, and delays in breach notification. Most of these are because of failure to maintain logs, inability to reconstruct digital events, no formal breach investigation reporting, and incomplete evidence collection during investigations. As healthcare breaches require detailed forensic timelines as per HIPAA, lack of such evidence directly results in penalties.
Few of latest research shows that non-compliance costs 2.71 times more than maintaining proper controls when accounting for fines, settlements, business disruption, and reputational damage.
Organizations that cannot produce timely, complete, and defensible digital evidence - which includes forensic reports, logs, timelines, and breach analysis - face severe financial and regulatory consequences.
"Cyber incidents pose various risks to organizations, including legal and reputational challenges. A digital forensics report acts as a crucial resource, providing legally defensible evidence, ensuring compliance, and fostering trust. It aids in enhancing long-term security measures, enabling organizations not only to recover but also to learn and improve from incidents, ultimately emerging stronger.
SecureClaw provides enterprise-grade Digital Forensics-as-a-Service (DFaaS), enabling organizations to rapidly investigate cyber incidents with precision, clarity, and compliance-ready evidence."
Dr. Shekhar A Pawar CEO, SecureClaw
A Few of the Worldwide Forensics Compliance and Cyber-Incident Reporting
In the current interconnected environment, cyber incidents pose significant business risks, prompting governments to enforce stricter reporting requirements and enhanced digital-forensics preparedness from organizations. Regulations, including the EU's GDPR, India's DPDP Act, and U.S. CIRCIA, impose tight deadlines for breach reporting and forensic evidence production, often requiring compliance within hours. This shift emphasizes mandatory transparency and accountability, necessitating organizations to maintain forensic logs, conduct rapid assessments, and swiftly communicate incidents to regulators and stakeholders. Understanding these reporting obligations is crucial for legal protection and fostering stakeholder trust.
The below table is highlighting a few well-known compliances and their expectations for incident reporting.
| Compliance Name | Country / Region | Reporting Timeline | Forensic / Reporting Expectations |
|---|---|---|---|
| GDPR (General Data Protection Regulation) | European Union | 72-hour notification for personal data breaches. | Requires breach assessment, logs, impact analysis, and justification for delays. |
| UK GDPR & NIS Regulations | United Kingdom | 72 hours (UK GDPR); "Without undue delay" under NIS. | Maintain logs, provide evidence of impact, and complete incident documentation. |
| DPDP Act (Digital Personal Data Protection Act) | India | Notify regulator and users without undue delay. | Requires audit trails, evidence of compliance, and support for forensic investigation. |
| CERT-In Cyber Incident Reporting Directive | India | Report incidents within 6 hours of detection. | Requires 180-day log retention and submission of technical incident evidence. |
| CIRCIA (Critical Infrastructure Act) | United States | Report incidents to CISA within 72 hours; ransomware payments within 24 hours. | Submit logs, intrusion evidence, and detailed forensic analysis. |
| SEC Cybersecurity Disclosure Rule | United States | Disclose material cyber incidents within 4 business days. | Provide forensic-backed impact details, timelines, and compromised system evidence. |
| HIPAA (Health Insurance Portability and Accountability Act) | United States | Notify affected individuals within 60 days. | Maintain forensic logs, PHI exposure documentation, and audit trails. |
| PIPEDA (Personal Information Protection and Electronic Documents Act) | Canada | Notify "as soon as feasible" after confirming breach. | Maintain breach records for 24 months to support forensic investigations. |
| LGPD (Lei Geral de Proteção de Dados) | Brazil | Notify authorities and users within a reasonable time. | Document breach analysis, logs, and mitigation steps. |
| PIPL (Personal Information Protection Law) | China | Immediate notification for serious data leaks. | Provide detailed forensic findings, impact scope, and corrective actions. |
| NDB Scheme (Notifiable Data Breaches) | Australia | Assess incidents within 30 days; notify promptly. | Conduct forensic assessment of what data was accessed or compromised. |
| APPI (Act on Protection of Personal Information) | Japan | Prompt notification for serious breaches. | Provide investigation results, including what data was exposed. |
| PDPA (Personal Data Protection Act) | Singapore | Notify regulator within 3 days of identifying a breach. | Submit forensic findings, compromised datasets, and mitigation actions. |
Why Every Organization Must Prepare a Digital Forensics Report After a Cyber Incident?
A digital forensics report serves as a strategic, legal, and operational asset, offering crucial evidence post-cyber incident. It is essential for understanding incidents, fulfilling legal requirements, enhancing security, and maintaining stakeholder trust. Key aspects include compliance, trust, legal protection, strategic improvement, insurance, and future readiness.
-
Compliance and Regulatory Accountability:
Modern regulations require organizations to demonstrate the circumstances of incidents and the affected systems, with digital forensics playing a crucial role in gathering and presenting evidence. Forensic investigations can have legal implications, necessitating proper evidence handling and compliance with local laws. Forensic readiness is essential for legally acceptable evidence collection. A digital forensics report is vital for protecting organizations against negligence claims, fulfilling audit requirements, and adhering to incident-reporting obligations under data protection laws.
-
Restoring and Maintaining Stakeholder Trust:
Customers and stakeholders expect transparency following a cyber incident. A detailed forensics report clarifies what was breached and the actions taken, aiding in confidence restoration. Digital forensics reveals deleted files and unauthorized access, allowing leaders to communicate effectively with stakeholders. Clear communication is essential to prevent misinformation, reassure customers, and safeguard brand reputation.
-
Legal Defense, Evidence Preservation and Litigation Support:
In cyber incidents, organizations often encounter lawsuits, insurance claims, regulatory inquiries, or criminal investigations. Digital forensics is critical for legally defensible evidence collection, ensuring chain-of-custody documentation is preserved. Strict evidence-handling processes are necessary as forensic findings may be presented in court. Forensic readiness enables efficient, tamper-proof evidence gathering, essential for organizations to withstand legal scrutiny. Without a thorough forensics report, organizations risk losing legal cases, incurring fines, or failing to demonstrate their innocence or due diligence.
-
Insurance Claims, Financial Recovery and Risk Assessment:
Cyber insurance providers require organizations to submit detailed, timestamped forensic reports to validate claims for breaches, ransomware, or fraud. Digital forensics helps insurers assess payouts by revealing attack vectors, system impacts, financial losses, and incident timelines. Effective forensic preparation can significantly reduce breach-related costs. A forensic report is crucial as it often dictates the outcome of compensation claims, affecting whether an organization receives full, partial, or no reimbursement.
-
Understanding the Root Cause and Preventing Future Attacks:
Digital forensics plays a crucial role in root-cause analysis, going beyond restoring operations to uncover how attackers infiltrated systems and which vulnerabilities were exploited. It enhances incident response, visibility, and security posture, while identifying advanced threat patterns and gaps that go unnoticed in regular monitoring. Ultimately, a forensics report shifts an incident from a mere disruption to a strategic opportunity for reinforcing defenses.
-
Protecting Organizational Reputation and Business Continuity:
A mishandled cyber incident can cause significant long-term damage and operational disruption. Digital forensics mitigates these risks by providing clear facts for rapid, evidence-based decisions, helping organizations identify unusual activities and respond quickly to protect operations. Speed and accuracy in crisis management are crucial for minimizing reputational harm.
-
Supporting Internal Investigations and HR Actions:
Cyber incidents can involve not only external attackers but also negligent or malicious insiders. Digital forensics plays a crucial role in uncovering internal activities, device usage, and deleted content to identify potential misuse or policy violations. It helps retrieve evidence like deleted files and internet history, which aids organizations in taking disciplinary action, mitigating future risks, and preserving workplace integrity.
"Digital forensics can no longer be an afterthought. With SecureClaw DFaaS, we empower organizations to uncover the truth behind every incident-faster, smarter, and with evidence that stands the test of compliance and accountability."
Dr. Shekhar A Pawar CEO, SecureClaw
SecureClaw's Digital Forensics-as-a-Service (DFaaS)
SecureClaw's DFaaS empowers leadership with clear visibility into cyber incidents, providing timely forensic reporting and actionable intelligence to strengthen governance and resilience.
-
Strengthening Enterprise Security Through Evidence-Driven Insight:
Modern organizations now face a heightened threat landscape where cyber incidents are inevitable. Digital forensics has become crucial for businesses to analyze past cyber events, identify causes, and enhance prevention measures. SecureClaw's Digital Forensics-as-a-Service enables precise investigation of digital incidents, evidence preservation, and uncovering of attack paths, thereby improving long-term resilience. This approach supports industry insights that emphasize the importance of digital forensics in ensuring thorough analysis and maintaining legal and procedural accuracy.
-
A Complete Forensic Investigation Framework - Delivered as a Service:
SecureClaw delivers a comprehensive forensic capability designed to meet the demands of modern enterprise environments. Our DFaaS platform enables organizations to identify, collect, preserve, and analyze digital evidence across computers, networks, cloud assets, and mobile devices. As digital infrastructures expand, so does the need for a forensics approach that can handle diverse sources such as system logs, deleted files, user activity records, and traces of unauthorized access - all crucial elements in today's forensic investigations.
-
Legal-Grade Evidence Handling and Compliance Assurance:
SecureClaw emphasizes the importance of following strict forensic protocols in cyber incident investigations. This approach addresses legal, regulatory, and insurance implications while ensuring that evidence gathered is defensible in audits, disputes, and court proceedings. Adhering to established legal authority and evidence-handling standards helps organizations maintain compliance and avoid errors that could jeopardize their legal standing.
-
Preparedness Through Forensic Readiness:
Proactive organizations are adopting forensic readiness to quickly and legally capture and analyze digital evidence during incidents. SecureClaw's DFaaS enhances this by optimizing logging, data retention, and monitoring, leading to improved incident response, regulatory compliance, and mitigation of financial and reputational damages from cyber events. Evidence shows that forensic readiness is essential for efficient evidence gathering and cost-effective breach management, making it a key component of modern security strategies.
-
Actionable Insights for Stronger Cybersecurity:
Digital forensics is crucial for enhancing a company's security maturity, as it helps transform forensic findings into actionable intelligence. SecureClaw aids organizations in understanding attack vectors, eliminating vulnerabilities, and improving defensive strategies. This approach aligns with expert guidance, emphasizing that digital forensics identifies cyber threats, uncovers attack methods, and enhances visibility within digital ecosystems, ultimately preventing future incidents.
Process of SecureClaw's Digital Forensics-as-a-Service (DFaaS)
SecureClaw's DFaaS empowers leadership with clear visibility into cyber incidents, providing timely forensic reporting and actionable intelligence to strengthen governance and resilience.
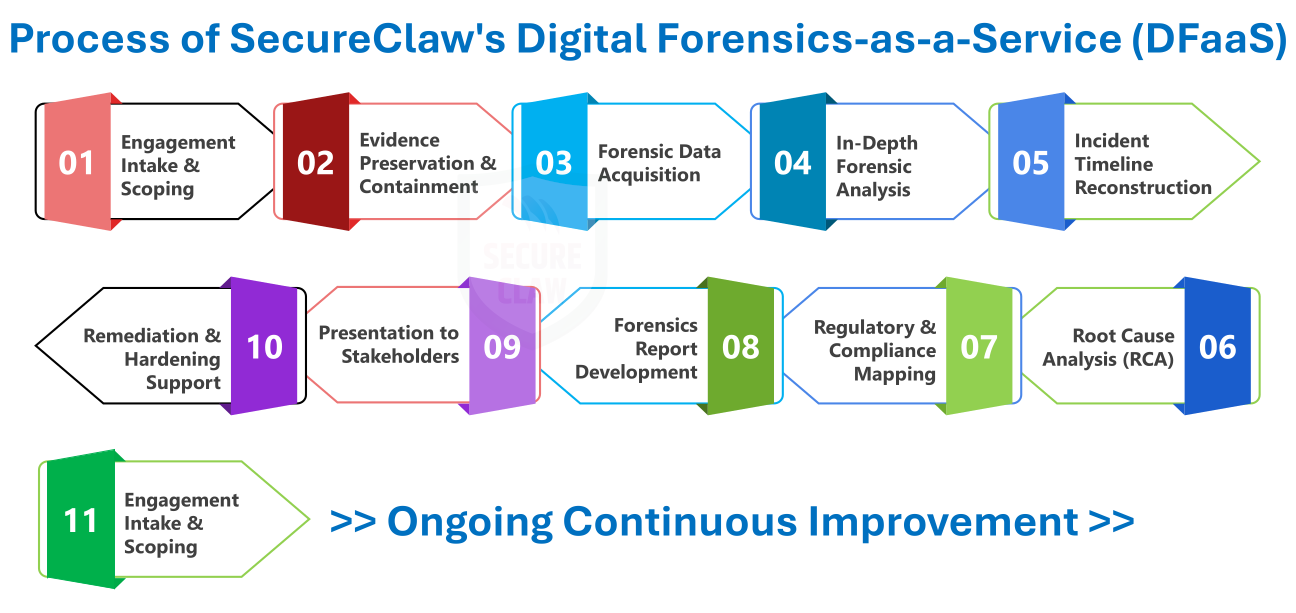
- Engagement Intake and Scoping
- Understand the incident background, affected systems, timeline, and business impact.
- Define scope, urgency, access requirements, and expected deliverables.
- Evidence Preservation and Containment
- Isolate compromised systems without altering evidence.
- Create forensically sound disk images and memory dumps.
- Document chain of custody for all evidence.
- Forensic Data Acquisition
- Collect data from endpoints, cloud platforms, servers, network devices, and Software as a Service (SaaS) systems.
- Use industry-standard imaging tools and secure acquisition methods.
- In-Depth Forensic Analysis
- Identify attack vectors, malicious activities, and lateral movement.
- Analyze logs, artifacts, deleted data, malware behavior, and Indicator of Compromises (IoCs).
- Reconstruct attacker behavior across systems.
- Incident Timeline Reconstruction
- Build a minute-by-minute timeline of events.
- Highlight attacker actions, system responses, and data impact.
- Root Cause Analysis (RCA)
- Identify the exact cause of the incident and exploited weaknesses.
- Determine failing controls, process gaps, or human factors.
- Regulatory and Compliance Mapping
- Align findings with DPDP, CERT-In, GDPR, HIPAA, PCI-DSS, and industry frameworks.
- Advise on mandatory breach notification requirements and timelines.
- Forensics Report Development
- Prepare a detailed, court-ready forensic report.
- Include scope, methodology, evidence inventory, findings, IoCs, timelines, RCA, and impact analysis.
- Provide recommendations to prevent recurrence.
- Presentation to Stakeholders
- Deliver executive briefing and technical deep-dive sessions.
- Support legal, compliance, IT, and security teams with actionable insights.
- Remediation and Hardening Support
- Recommend and assist with patching, control strengthening, and architecture improvements.
- Enhance monitoring, detection, and access management practices.
- Post-Incident Forensic Readiness Planning
- Develop forensic-ready logging and evidence retention policies.
- Implement IR playbooks, standard operating procedures (SOPs), and tabletop exercises.
- Train internal teams on evidence preservation best practices.
Cyber threats have evolved to be more sophisticated and persistent, necessitating businesses to not only implement preventive security measures but also to have the ability to analyze attacks comprehensively. SecureClaw's Digital Forensics-as-a-Service provides this capability by offering investigative insights and structured evidence analysis. Digital forensics is crucial in reducing damage, ensuring accountability, and restoring trust in systems affected by cybercrime, as attackers increasingly target various digital assets.